5 Cyber Security Threats That Are Lurking on Social Media


The ease of using social media has opened the doors for hackers to attack their users. Billions use social media every day, and they are spread out across multiple platforms. As cyber security threats get more dangerous, users have to become smarter about how they interact with new technologies.
1. Misinformation
Misinformation is one of the oldest social engineering techniques in the world. Companies like IT support Brisbane are competent enough to stop the threat before it takes root. For other unlucky companies, the end result is much more severe. And for individuals, social media misinformation can cause life-long damage. Misinformation has threat levels ranging from minor to major, and can even come from normally approved sources. A good example of misinformation is doxing or publishing the private information of someone innocent of malicious intent.
2. Identity Theft
This is a big threat and happens more than you expect. Once an attacker steals your identity, they can pretend to be you for multiple reasons. This includes opening bank accounts, buying things online, trying out a new line of credit, and even committing crimes using your identity. An attacker can steal your credential by creating a fake login page to a social media website. Once you enter the information, they can log in and get whatever information is stored on the official server. Two-step authentication is a good deterrent to stop identity theft on social media platforms.
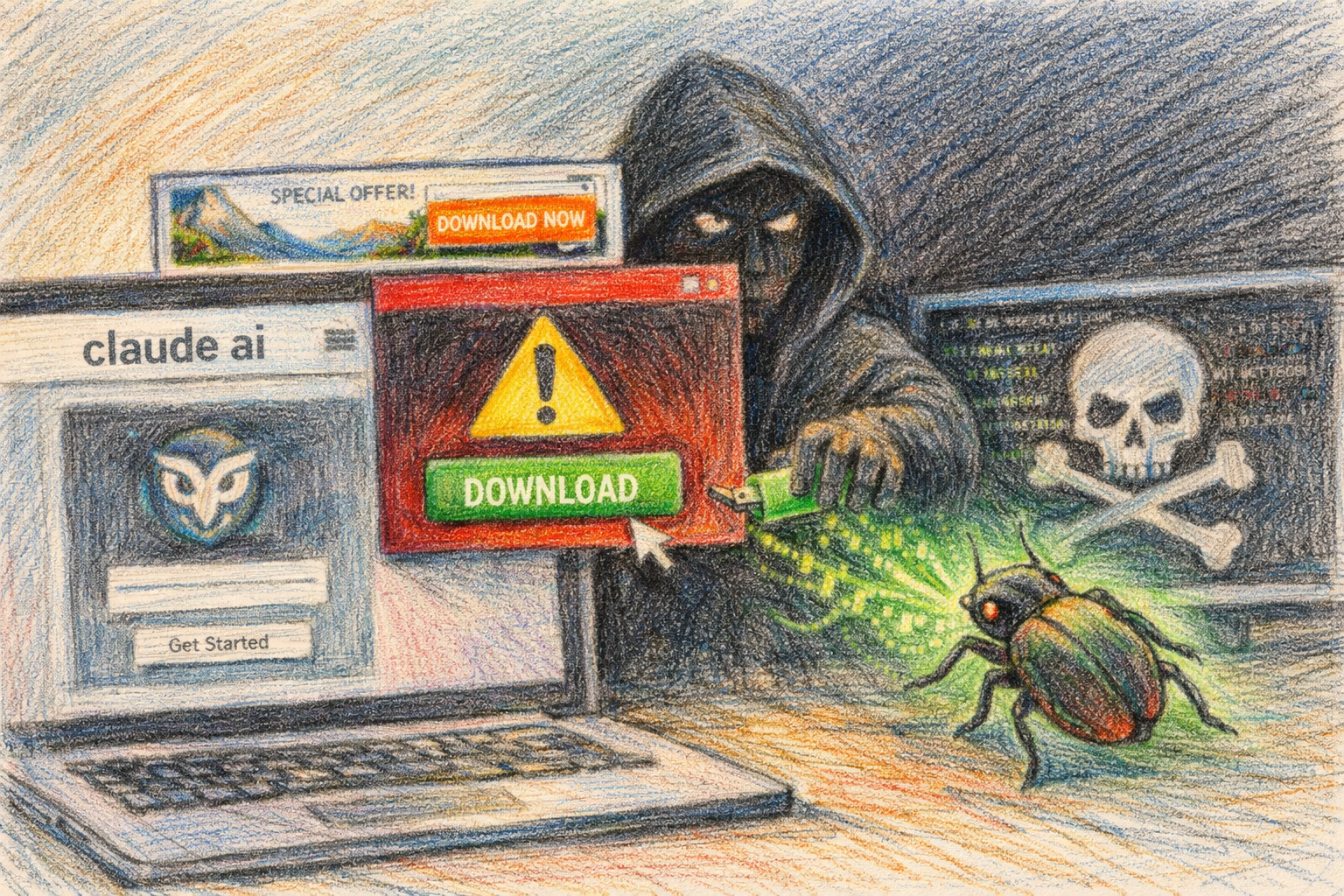
3. Malware
Malware is a common problem among users that share a lot on social media. Any file you download from an unknown source can be embedded with a virus. Once it is on your phone or computer, the virus gains full access to your contacts. It then has the ability to send and share messages posing as you, the original contact. This leads to your friends and family downloading the same virus, and slowly spreading it to their own contacts. If you don’t know the source, then don’t share or download it on social media.
4. Phishing
Phishing is when the attacker tricks you into voluntarily sending your information. A simple email saying you need to change social media logins can quickly destabilize your entire online identity. Never click on links in emails that aren’t official. Pay close attention to the email address as simple misspellings are easy to miss when you’re in a rush. Once you spot one, there is a good chance there will be many more that come after it.
5. Data Breach
Data breaches affect the entire userbase of an organization, from workers to clients. This can happen when a security flaw isn’t patched in the company’s system. It can also happen when a single worker uses a proxy to override the company’s strict social media protocols. Once an organization is targeted, it takes an incredible number of resources to right the ship.
Handle It Properly
There is no reason to hit the panic button if you use social media. Cyber security threats can be handled when you’re aware of the dangers. With the right attitude, you can thwart the nefarious goals of any attacker.