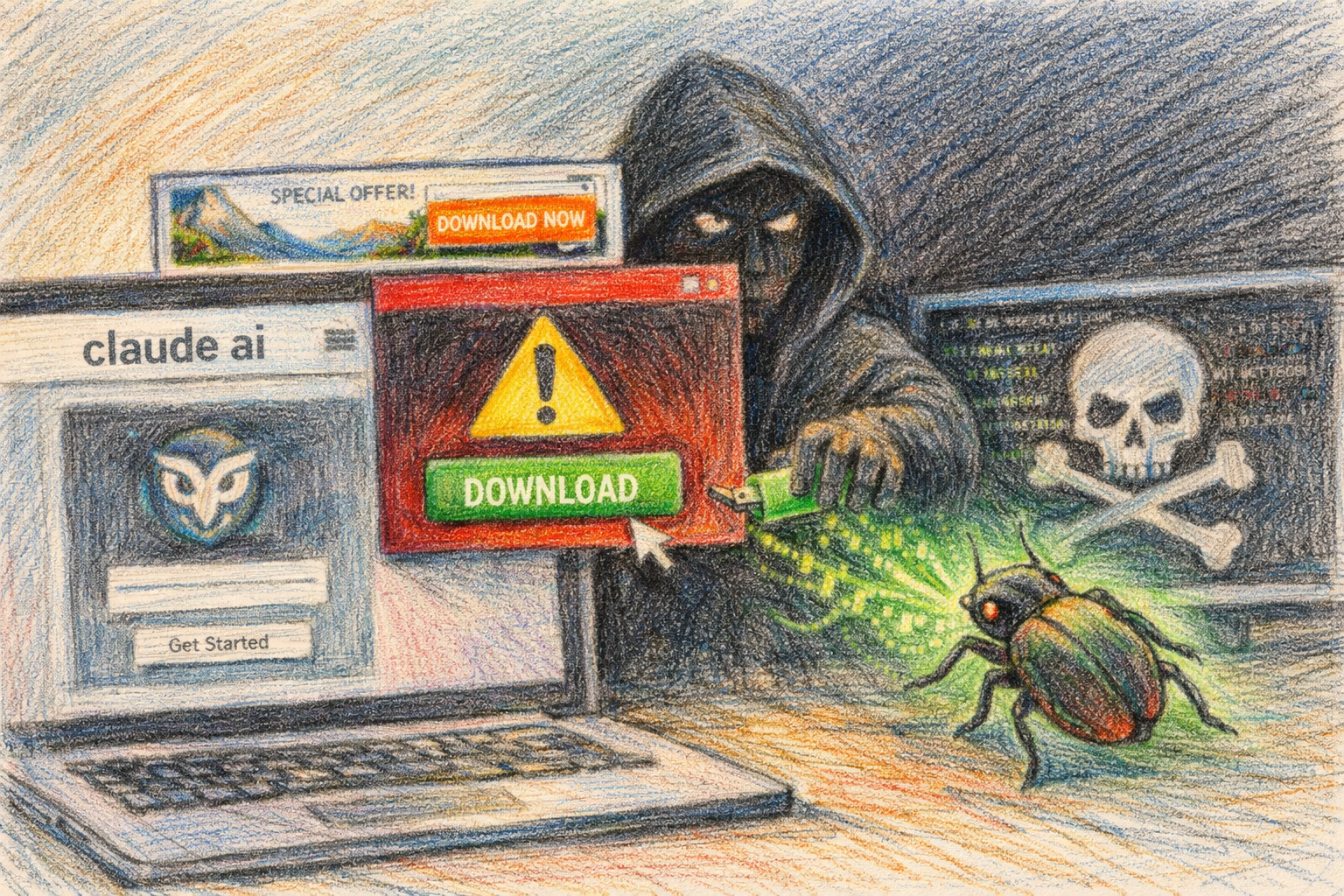
Fake Claude installer steals dev creds, bypasses Chrome ABE
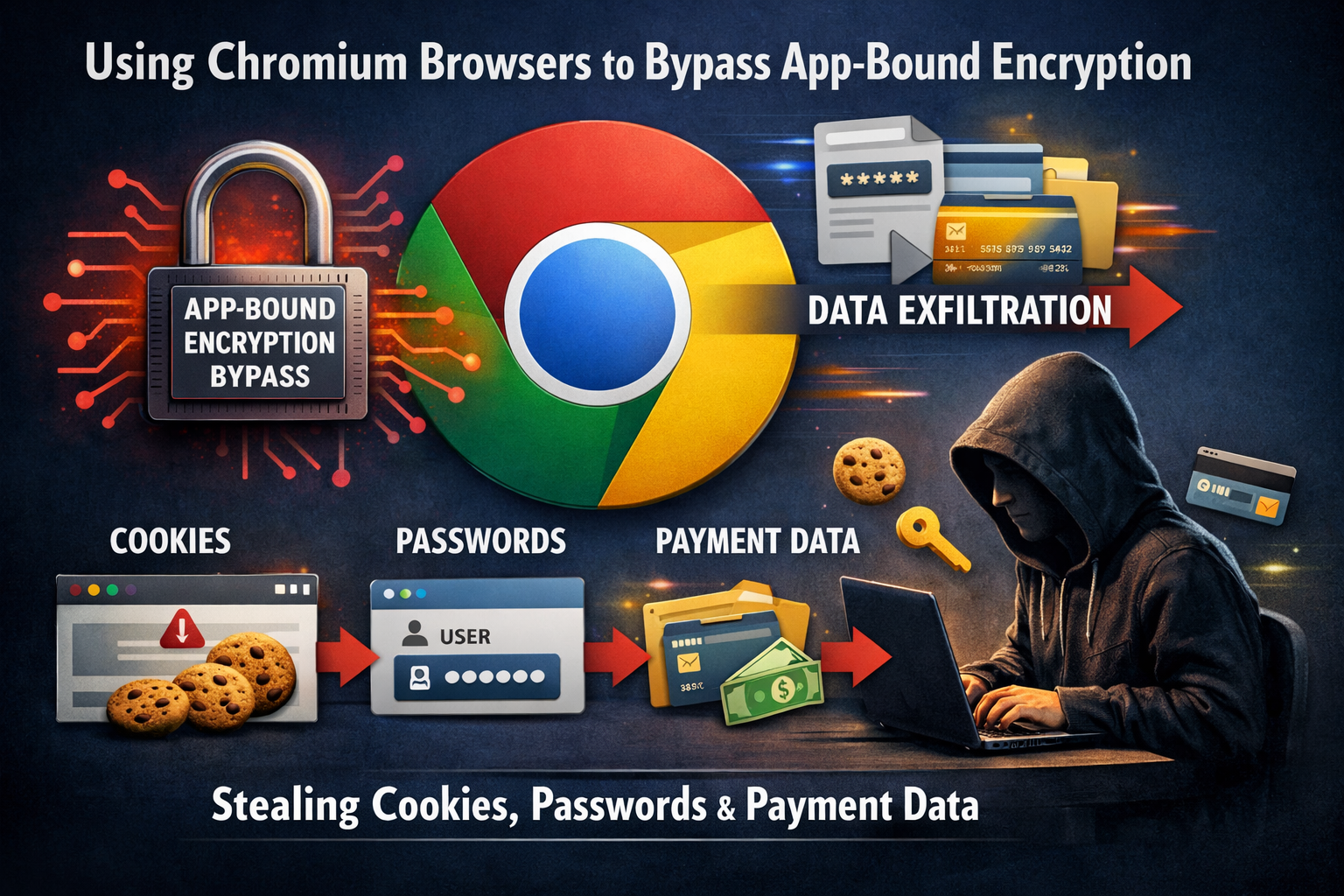
Cybersecurity researchers have uncovered a new information stealer malware targeting software developers through fake Claude Code installation pages appearing in sponsored search results. The previously undocumented information stealer has been distributed through fake Claude Code installation pages, hijacking Chromium browsers to bypass App-Bound Encryption and exfiltrate cookies, passwords and payment data from developer workstations. The campaign was detailed on May 11 by Ontinue’s Cyber Defense Center.
How the Attack Works
The attack relies on developers searching for “install claude code,” and selecting a sponsored result that leads to a lookalike Claude Code installation page. The fake installation page mimics legitimate one-line installer commands commonly used in software development workflows, but substitutes malicious PowerShell code in place of the authentic installer.
The page downloads and executes Anthropic’s authentic installer, but the malicious instruction isn’t stored in the file itself, but instead rendered into the HTML of the landing page. This technique allows the malware to evade automated security scanners. “Automated scanners, URL reputation services, and any skeptical reviewer who simply curls the URL therefore observe clean PowerShell delivered from a Cloudflare-fronted domain bearing a valid Let’s Encrypt certificate,” the researchers wrote.
The attack runs across three domains, all registered within six days of each other in April, and all fronted through Cloudflare.
Advanced Encryption Bypass Technique
What makes this malware particularly dangerous is its ability to bypass Chromium’s App-Bound Encryption (ABE), a security feature designed to protect sensitive user data. The attacks also abuse the IElevator2 COM interface, which is Chromium’s elevation service used to handle App-Bound Encryption (ABE), specifically for encrypting and decrypting sensitive user data like cookies and passwords.
A transcription error in the embedded Edge IElevator2 IID, with two nibbles transposed in the Data3 field, causes the initial call to fail silently and trigger a fallback to the legacy IElevator interface. Ontinue highlighted that the malformed identifier doubles as a high-confidence detection signature.
The payload exfiltrates decrypted cookies, passwords, and payment methods from Chromium-based browsers such as Google Chrome, Microsoft Edge, Brave, Vivaldi, and Opera.
Recently Developed Threat
Ontinue’s compile-date evidence places the sample’s construction within 60 days of the Chrome 144 release in January 2026, indicating an actively maintained development effort tracking upstream Chromium changes. This suggests the threat actors are actively updating their malware to keep pace with browser security developments.
The loader established persistence via a Windows scheduled task that polled the operator’s C2 every minute and exited early if the host’s region matched an exclusion list covering Iran, Russia and other Commonwealth of Independent States (CIS) members, among others.
Unknown Malware Family
The malware hunters compared the malware against published reporting for several stealers, including Lumma, StealC, Vidar, EddieStealer, Glove Stealer, Katz Stealer, Marco Stealer, Shuyal, AuraStealer, Torg Grabber, VoidStealer, Phemedrone, Metastealer, Xenostealer, ACRStealer, DumpBrowserSecrets, DeepLoad, and Storm, and found no technical match.
The closest is Glove Stealer, first documented by Gen Digital in November 2024, which also abuses IElevator via a helper module communicating over a named pipe. However, the orchestration model differs from Glove in that it uses a “small native helper acting as a single-purpose ABE oracle, with all detection-visible activity pushed into PowerShell.”
Why Developers Are Targeted
Vineeta Sangaraju, AI research engineer at Black Duck, said the choice of target is what makes the campaign worth attention. Developers represent high-value targets because they often have access to sensitive code repositories, production environments, and customer data.
The campaign exploits the widespread developer practice of copying and running installation commands from documentation pages. Modern software installation frequently involves executing one-line commands, making developers accustomed to this workflow and potentially less cautious about verifying the source.
Broader Campaign Context
This newly documented stealer is part of a broader wave of attacks exploiting Claude AI’s popularity. Multiple security firms have reported various fake Claude installer campaigns throughout 2026, including the InstallFix campaign documented by Trend Micro in early May and a separate PlugX-based campaign distributing malware called Beagle through fake Claude-Pro websites.
The use of sponsored search results to distribute malware represents a growing threat vector, as users often trust paid advertisements at the top of search results to be legitimate. Security experts recommend that users verify they are downloading software only from official domains and consider hiding or skipping sponsored search results when looking for software downloads.
Key Facts
- Ontinue’s Cyber Defense Center detailed the campaign on May 11, 2026
- The malware bypasses Chromium’s App-Bound Encryption to steal cookies, passwords, and payment data
- Three malicious domains were registered within six days of each other in April 2026
- The malware was compiled within 60 days of Chrome 144’s January 2026 release
- The stealer does not match any previously documented malware family
- The attack excludes victims in Iran, Russia, and other CIS countries
Sources
- Infosecurity Magazine: Fake Claude Code Page Pushes PowerShell Stealer at Devs
- The Register: Cookie thieves caught stealing dev secrets via fake Claude Code installers
- Trend Micro: InstallFix and Claude Code: How Fake Install Pages Lead to Real Compromise
- BleepingComputer: Fake Claude AI website delivers new ‘Beagle’ Windows malware