Why is it Critical to Master the Principle of Least Privilege in Business Security?


Cloud security has become a paramount concern in the business world, and for a good reason. With data breaches and ransomware attacks becoming more common, it’s essential to do everything possible to protect your company’s sensitive information. One meaningful way to bolster your security posture is by mastering the principle of least privilege (POLP).
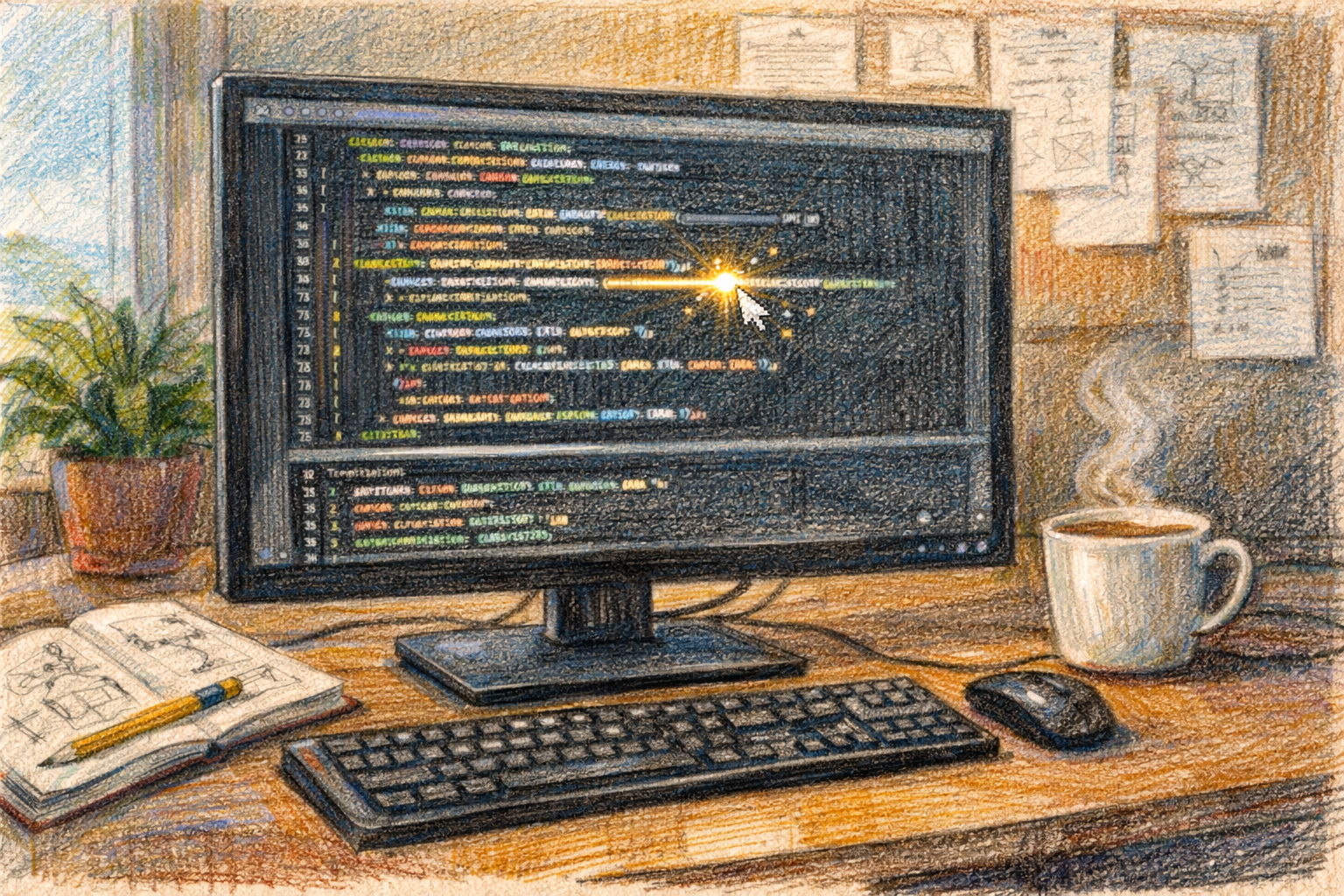
POLP is a security principle requiring users to be given the least amount of access necessary to perform their jobs. POLP offers a number of advantages for every company that uses it. One key benefit of the principle of least privilege example, is to minimize the damage caused by a security incident. It also helps protect against accidental or unauthorized access to data.
There are various reasons why POLP should be implemented in your organization. Here are some important ones.
1. Minimizes the Damage Caused by a Security Incident
If an attacker manages to hack into an employee’s account, their access will still be limited to what access level was authorized for that particular employee. Only the administrators have broad access to system resources and can quickly delete or modify data. By limiting users to their assigned privileges, you can minimize the negative impact of a security incident.
2. Enforces Compliance with Regulations
Your organization may need to comply with regulations that effectively mandate least privilege access. For example, if you operate in regulated industries like healthcare or finance, your company will need to implement POLP to remain compliant with federal law.
The Health Insurance Portability and Accountability Act (HIPAA) is one principle of least privilege and an example of a regulation that requires least privilege access.
3. Helps Prevent Accidental or Unauthorized Access to Data
If you don’t limit users to their assigned privileges, there is a greater risk of unauthorized access to data. It can happen when employees share passwords or when malicious actors gain access to your systems. By implementing POLP, you can help to reduce the risk of unauthorized access.
4. Helps Mitigate the Risk of Data Breaches
Data breaches can occur when an attacker manages to gain access to sensitive data. If this data is not adequately protected, the attacker can steal it, sell it, or use it for specific individual purposes. By implementing POLP, you can help reduce the risk of a data breach and protect your company’s confidential information.
5. Helps Improve Business Accountability
If you can track which users have accessed which data, it becomes easier to hold them accountable if something goes wrong. You can more easily determine which users had access to the data and what they did with it. By implementing POLP, you can improve accountability within your organization.
6. Improves Security Awareness
When users are restricted to their assigned privileges, it becomes easier to understand the importance of security. They can see how granting too much access can lead to negative consequences. By implementing POLP, you can help improve security awareness within your organization.
7. Increases Security
If you implement a least privilege deployment, it can be challenging for attackers to access your data. It makes your environment more secure and helps protect against different attacks. By implementing POLP, you can enhance the security of your systems and help reduce the risk of a security incident.
8. Delivers Greater ROI
POLP can help reduce the risk of data breaches and other types of security incidents. It enables you to deliver greater ROI because your organization is less likely to impact a security incident negatively.
Data breaches are expensive for companies, and a survey found that they cost an average of $3.8 million per incident.
9. Helps to Protect Against Reckless or Careless Behavior
If you implement POLP, employees might be less likely to take risks and engage in careless or reckless behavior. Employees and team members will only have the access they need for their specific role, which can make it harder to cause deeper harm.
10. Helps Align Security Measures with Business Objectives
Business and security teams would have the same goals in an ideal world. However, this isn’t always the actual case in many businesses today. In reality, business teams might be more focused on productivity and profitability, while security teams are tasked with restricting access to protect your company from a security incident. If you implement POLP, it can help to align these two teams and make it easier for them to work together.
The principle of least privilege mandates that you only grant users the necessary privileges or permissions they need to perform their specific tasks and no more. The least privilege enhances security by reducing potential attack surface areas and by minimizing damage from accidents.
As you can see, there are many reasons why it’s critical for businesses to master the principle of least privilege. By following this principle, you can minimize the damage caused by a security incident, enforce accountability, and help protect sensitive data. You can have a look at some examples of the principle of least privilege to gain better clarity.