Reasons to Track Incident Logs In Your Business Network


Networking is a crucial element in the modern-day world of entrepreneurship. It comes in handy in almost every business department, from IT to sales, customer service, and everything in-between. Now, as long as you utilize networking systems and applications in your business, each event or incident that takes place, the said network logs or documents it electronically. The network stores it in a central place in the form of log files.
These files serve as a rich source of information that you can use in many ways. Including inspiring creativity, influencing critical decision-making, enhancing network security, and boosting the overall revenue and growth of the business. Nonetheless, these benefits only work if you monitor incident logs.
Here are the top reasons to monitor incident logs in your business network.
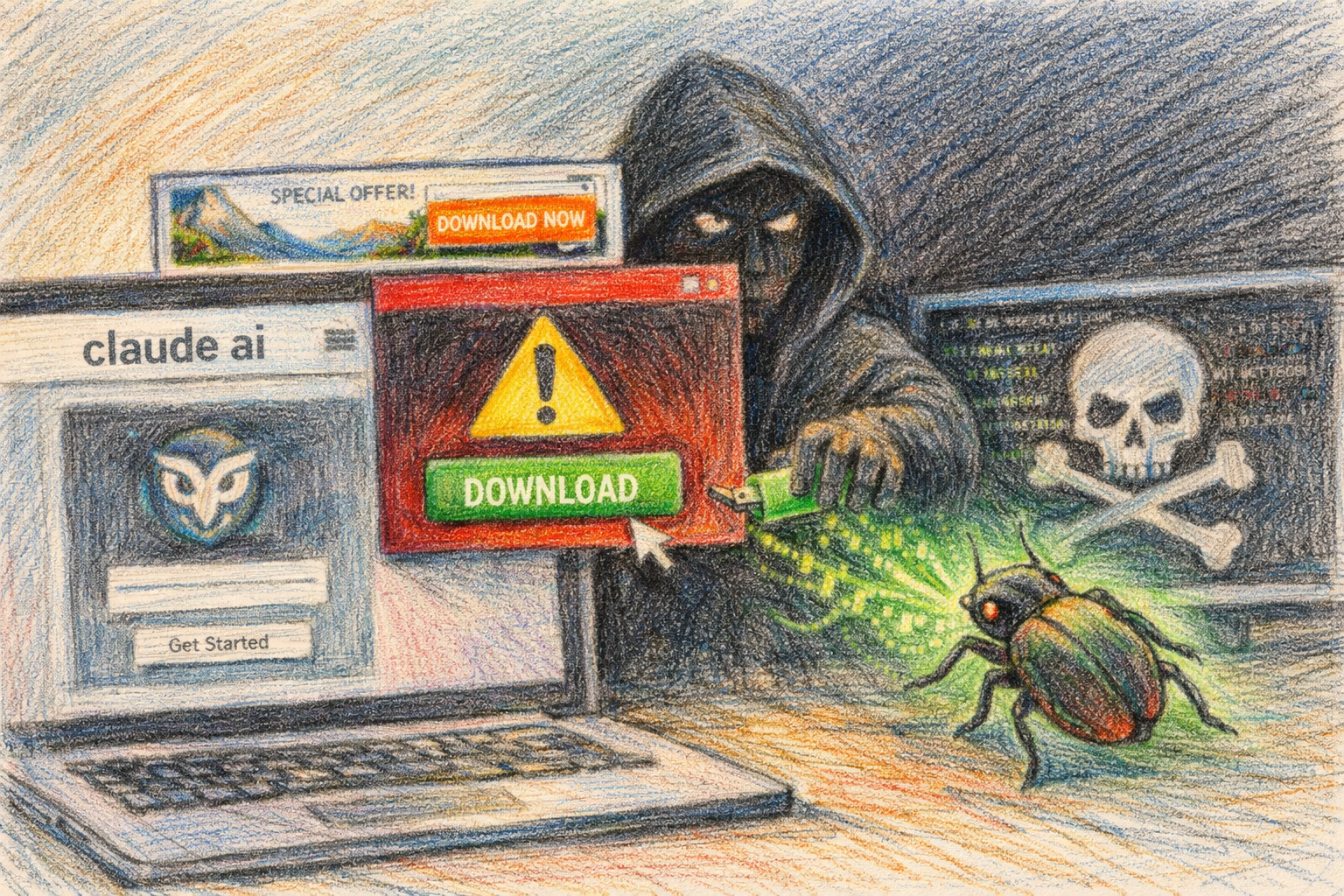
1. Enhancing Security
We live in an age where ill-intended hackers are always marauding looking for the next victim to defraud, defame, or steal sensitive information from. In many cases, business networks are often the target. However, if you track and analyze your network incident logs regularly, your business can stay a step ahead of data security threats and data breaches. Among the things you can accomplish by proactively tracking incident logs include:
- Optimizing filtering and blocking incoming traffic
- Prioritizing virus protection for email communication
- Monitoring unsuccessful authentication attempts
- Verifying configurations in firewalls
- Investigating security breaches
In a world where almost everything can be done remotely through digital communication devices, networking security is a crucial element as far as the success of your business.
2. Initiate Incident Response
Lastly, you can only find a solution for a problem if you can identify the problem. From cybersecurity threats to efficiency and compliance issues, incident log monitoring and analysis can reveal dozens of problems and challenges facing your business network.
But tracking and analyzing all log files in your business network manually can be a nightmare experience. It can be costly, time-consuming, and labor-intensive. This is why you should consider consolidating all your network logs in a centralized analyzer and monitoring system. With a good tool, you can get started with minimal effort and configuration skills.
3. Compliance
IT compliance is another critical aspect that impacts the success of most businesses in this age and day. However, to accept credit card payments, regulators require you to meet certain compliance standards. These are synonymously known as PCI compliance rules meant to ensure the safety of your customers’ money and sensitive information.
Employers are also required to ensure HIPAA compliance, which means protecting their clients’ health and insurance information and/or employees. As per OSHA guidelines on standards and best practices, any injuries or accidents that occur in the workplace should also be carefully and accurately documented. Thus, failure to ensure compliance with these and other specific rules may get your business in hot soup with the law.
By keeping track of network incident logs, you can detect and rectify any workplace compliance issues before they bring harm to your business. Keep the incident logs of data breaches, theft, or fraud attempts and continue to monitor them regularly. This way, your business can notify the respective authorities on time.
Conclusion
To sum it up, properly tracking and analyzing your network incident logs can benefit your business in many ways. It can help you prevent hacks and breaches, reduce expenses, and manage your employees better. Thus, your business can ensure regulatory compliance, ward off potential lawsuits, and even increase revenue.
Depending on the kind of business you run, tracking incident logs can also help improve customer service and retention. The above few points should be convincing enough to start tracking incident logs in your business network.