Top 10 Security Vulnerabilities in 2023: How to Safeguard Your Software


Picture this: your software, resulting from countless hours of hard work, has been breached. Your heart sinks. You scramble to rectify the damage, wishing you had been more proactive. But don’t worry, we’ve got your back! Here, we’ll unveil the top 10 security vulnerabilities in 2023 and arm you with the knowledge to safeguard your software. Ready? Let’s dive in!
The Evolving Landscape of Software Security
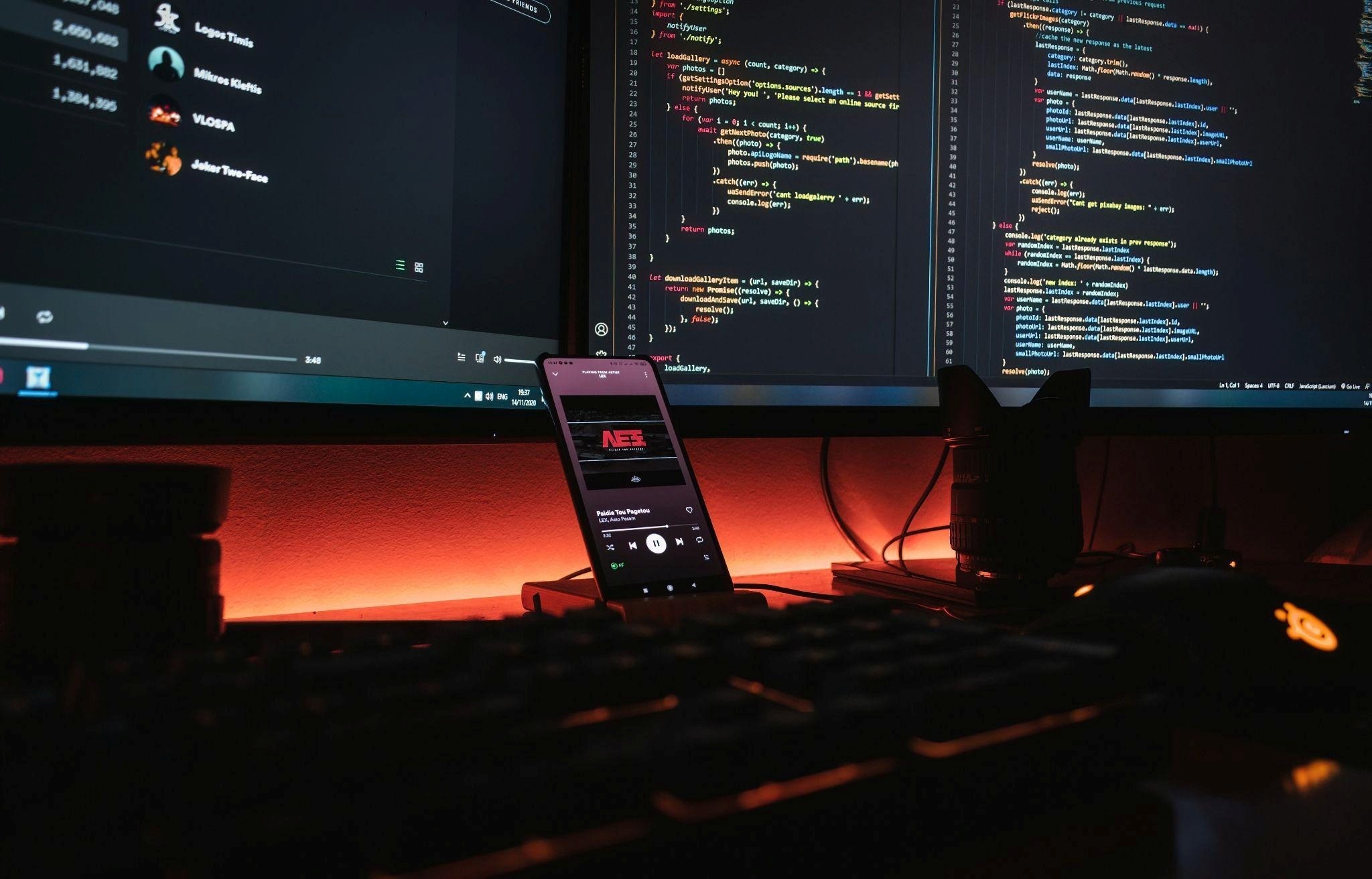
Before diving into the top 10 security vulnerabilities, let’s take a moment to understand the ever-changing landscape of software security. With the rapid advancement of technology, new risks and challenges constantly emerge, and hackers are evolving their tactics to keep up. As software developers, we must also adapt and continuously improve our defenses to stay ahead in this game of cat and mouse.
The rise of cloud computing, remote work, IoT devices, and artificial intelligence has only added to the complexity of securing our software. Gone are the days when simple firewalls and antivirus software were enough to protect our creations. Today, a multi-layered, proactive approach is vital to ensure the safety and integrity of our software.
Now that we have set the stage, let’s uncover the top 10 security vulnerabilities in 2023 and learn how to fortify and safeguard your software against these threats.
1. Injection Attacks
An oldie but a goodie, injection attacks still wreak havoc. Be it SQL, OS command, or LDAP injection, malicious code sneaks its way into your system. How do you fight back? Simple: validate, escape, and sanitize input data. Keep an eye on those API calls and watch out for dynamic queries.
2. Using Components with Known Vulnerabilities
Did you know? Using components with known vulnerabilities is like leaving your car unlocked with the keys inside. Don’t do it! Regularly update your components and follow the guide on CVE vulnerability by JFrog for the latest news. Your software is only as strong as its weakest link.
3. Broken Authentication
Flimsy authentication? Hackers rejoice! They exploit weak passwords, guessable usernames, and steal session tokens. Time to fortify your defenses and beef up and safeguard your security. Implement multi-factor authentication, enforce strong password policies, and limit login attempts. Don’t give hackers a free pass.
4. Sensitive Data Exposure
You wouldn’t leave your front door open, would you? Then why expose sensitive data? Encrypt data at rest and in transit, use secure protocols and mask critical information in order to safeguard your software. Remember, sensitive data is like the hidden treasure of your software kingdom—protect it with your life.
5. XML External Entities (XXE)
XML parsers, while helpful, can be an open invitation to XXE attacks. Crafty hackers exploit vulnerabilities to access sensitive data or execute remote code. How to stop them? Disable external entities, validate and sanitize inputs, and keep parsers updated. Don’t let XXE become the Achilles heel of your software.
6. Broken Access Control
Imagine a city without traffic signals—chaos! That’s what broken access control looks like. Unauthorized access to user accounts, data modification, and privilege escalation spell disaster. The fix? Implement role-based access control, validate user permissions, and keep a watchful eye on server-side access controls.
7. Security Misconfiguration
One small misconfiguration, one giant leap for hackers. Default settings, incomplete patches, and unprotected files are low-hanging fruit. Regularly update and harden your software, disable unnecessary features, and keep a tight lid on error messages. In short, keep your software shipshape.
8. Cross-Site Scripting (XSS)
XSS, the bane of web applications. Crafty attackers inject malicious scripts, steal session cookies, and wreak havoc. Fear not! Employ Content Security Policy (CSP), validate and sanitize user inputs, and escape untrusted data. Let your software be an impenetrable fortress.
9. Insecure Deserialization
Deserialization, like a double-edged sword, cuts both ways. Deserialize untrusted data, and you open the door to remote code execution and data tampering. Stay vigilant! Implement digital signatures, restrict deserialization, and be wary of user-supplied data. Keep your guard up.
10. Insufficient Logging and Monitoring
Blind spots in logging and monitoring are a hacker’s playground and must be cleaned up to safeguard your software. When attacks go unnoticed, the damage multiplies. So, what’s the solution? Implement comprehensive logging and monitoring, set up timely alerts, and routinely review logs. Keep a hawk’s eye on your software’s pulse.
Conclusion
There you have it, the top 10 security vulnerabilities in 2023 to safeguard your software. But the battle doesn’t end here. Remember, software security is an ever-evolving landscape. Stay informed, adapt, and be proactive. Learn from others’ mistakes and make your software a fortress that even the most seasoned hackers can’t breach.
So, what are you waiting for? It’s time to roll up your sleeves, tighten your defenses, and safeguard your software. After all, an ounce of prevention is worth a pound of cure. Happy securing!