Malvertising Uses Fake Claude Site to Deliver Beagle
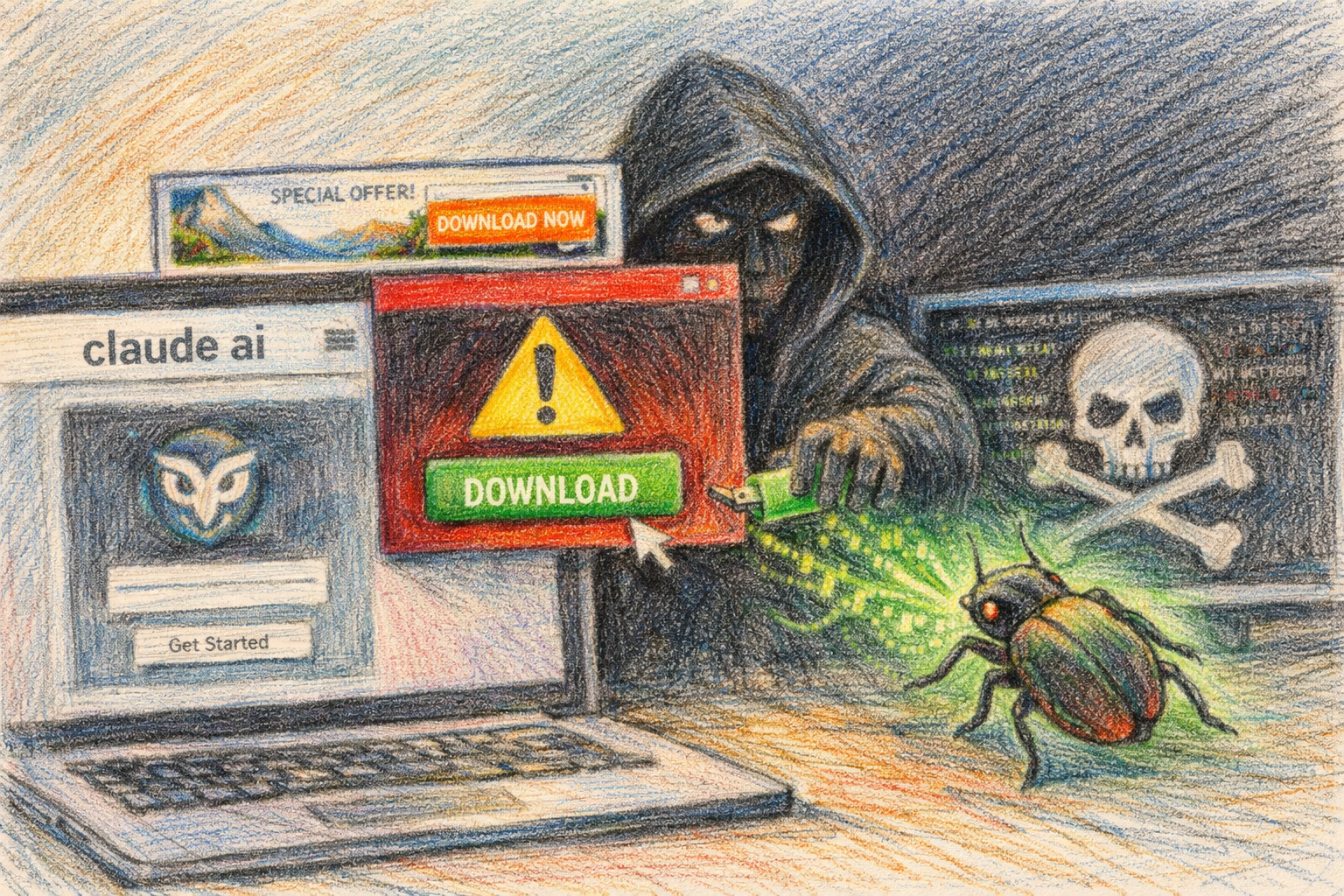
Cybersecurity researchers have uncovered an active malvertising campaign that uses a fake Claude AI website to distribute a previously undocumented Windows backdoor dubbed Beagle. Sophos X-Ops researchers have documented an active malvertising campaign using a fake Claude AI website to distribute a previously undocumented Windows backdoor named Beagle. The campaign was initially discovered by Malwarebytes and reaches victims through Google sponsored search results and SEO poisoning.
How the Attack Works
The malicious domain claude-pro[.]com impersonates Anthropic’s Claude interface using similar colors and fonts, but with non-functional links that redirect to the front page. The only working element is a download button for a 505MB archive named Claude-Pro-windows-x64.zip, promoted as a high-performance relay service for Claude Code developers.
When victims download and execute the file, the malware uses a sophisticated infection chain. The downloaded archive contains an MSI installer that drops three files into the Windows Startup folder: NOVupdate.exe, a legitimately signed G Data antivirus updater; avk.dll, a malicious DLL; and an encrypted data file named NOVupdate.exe.dat.
The attack uses DLL sideloading to abuse the trusted G Data binary into loading the malicious DLL, which executes an in-memory DonutLoader that fetches the Beagle backdoor. The installed Claude application functions normally, concealing the compromise from users.
Beagle Backdoor Capabilities
The Beagle backdoor, which is distinct from the older Delphi-based Beagle worm documented in 2004, provides attackers with comprehensive remote access to infected systems. Beagle supports eight commands covering shell execution via CMD and PowerShell, file upload and download, directory listing, folder creation, file renaming, directory deletion, and self-removal.
It communicates with a command-and-control server at license[.]claude-pro[.]com over TCP port 443 or UDP port 8080, encrypting traffic with a hardcoded AES key. The malware contains a hardcoded AES key (beagle_default_secret_key_12345!), which researchers used to identify related samples.
Campaign Timeline and Infrastructure
Analysis of the campaign infrastructure reveals that the operators have been active for several months. The researchers assessed that the site is part of an active malvertising campaign and traced the hosting infrastructure to a server set up in March 2026. Sophos found related samples from February through April 2026 using the same decryption key, and the operators were observed switching bulk email providers from Kingmailer to CampaignLark in April to stay ahead of blocklists.
Sophos researchers also discovered connections to additional malicious infrastructure. Even more interestingly, our research suggests another linked hosting server (178[.]128[.]108[.]89), associated with a domain called vertextrust-advisors[.]com.
Potential Links to PlugX Operations
The infection chain employed in this campaign bears strong similarities to techniques used by other threat actors. Sophos initially suspected a PlugX variant given the combination of a G DATA-signed binary, an avk.dll sideload and an encrypted data file, all of which were linked to PlugX in a February 2026 Lab52 report. The delivery of a different payload led researchers to consider that the threat actor may have retooled an established infection chain or imitated one used by another group.
The same sideloading chain has been linked to PlugX activity, though Sophos could not confirm attribution. However, those samples infected machines via different attack chains, including Microsoft Defender binaries, AdaptixC2 shellcode and a decoy PDF, and impersonating update sites from multiple security vendors (e.g., CrowdStrike, SentinelOne, and Trellix).
Protection Recommendations
Security experts recommend several steps to protect against this threat. Users should verify that they are visiting the legitimate Claude website at claude.ai before downloading any software. The threat exploits the growing popularity of AI tools, with attackers crafting convincing lures that appear in sponsored search results above legitimate listings.
The campaign represents an evolution in malvertising tactics targeting the technology sector. “Most of the techniques described here are relatively well known and have been seen before, from spoofing a legitimate installer website to side loading using a signed executable. Interestingly enough what is unusual is that it also installs a working copy of Claude which is rather large,” said Max Gannon, cyber intelligence team manager at Cofense.
Key Facts
- The malicious domain claude-pro[.]com distributes a 505MB fake Claude installer containing the Beagle backdoor
- Campaign infrastructure was established in March 2026, with related samples dating back to February 2026
- The backdoor communicates using hardcoded AES encryption key “beagle_default_secret_key_12345!”
- Attackers switched from Kingmailer to CampaignLark email services in April 2026 to evade blocklists
- The infection chain uses DLL sideloading via a signed G Data antivirus updater to bypass security controls
- Victims reach the fake site through Google sponsored search results and SEO poisoning techniques
Sources
- Security Boulevard: Fake Claude AI Website Delivers New Beagle Windows Backdoor via Malvertising
- Sophos: Donuts and Beagles: Fake Claude site spreads backdoor
- BleepingComputer: Fake Claude AI website delivers new ‘Beagle’ Windows malware
- Infosecurity Magazine: Fake Claude AI Site Drops Beagle Backdoor on Windows Users
Sources
- Fake Claude AI Website Delivers New Beagle Windows Backdoor via Malvertising – Security Boulevard
- Donuts and Beagles: Fake Claude site spreads backdoor | SOPHOS
- Fake Claude AI Site Drops Beagle Backdoor on Windows Users – Infosecurity Magazine
- Fake Claude AI website delivers new ‘Beagle’ Windows malware
- Claude users beware, hackers are using a fake website to dupe developers and deliver malware | IT Pro