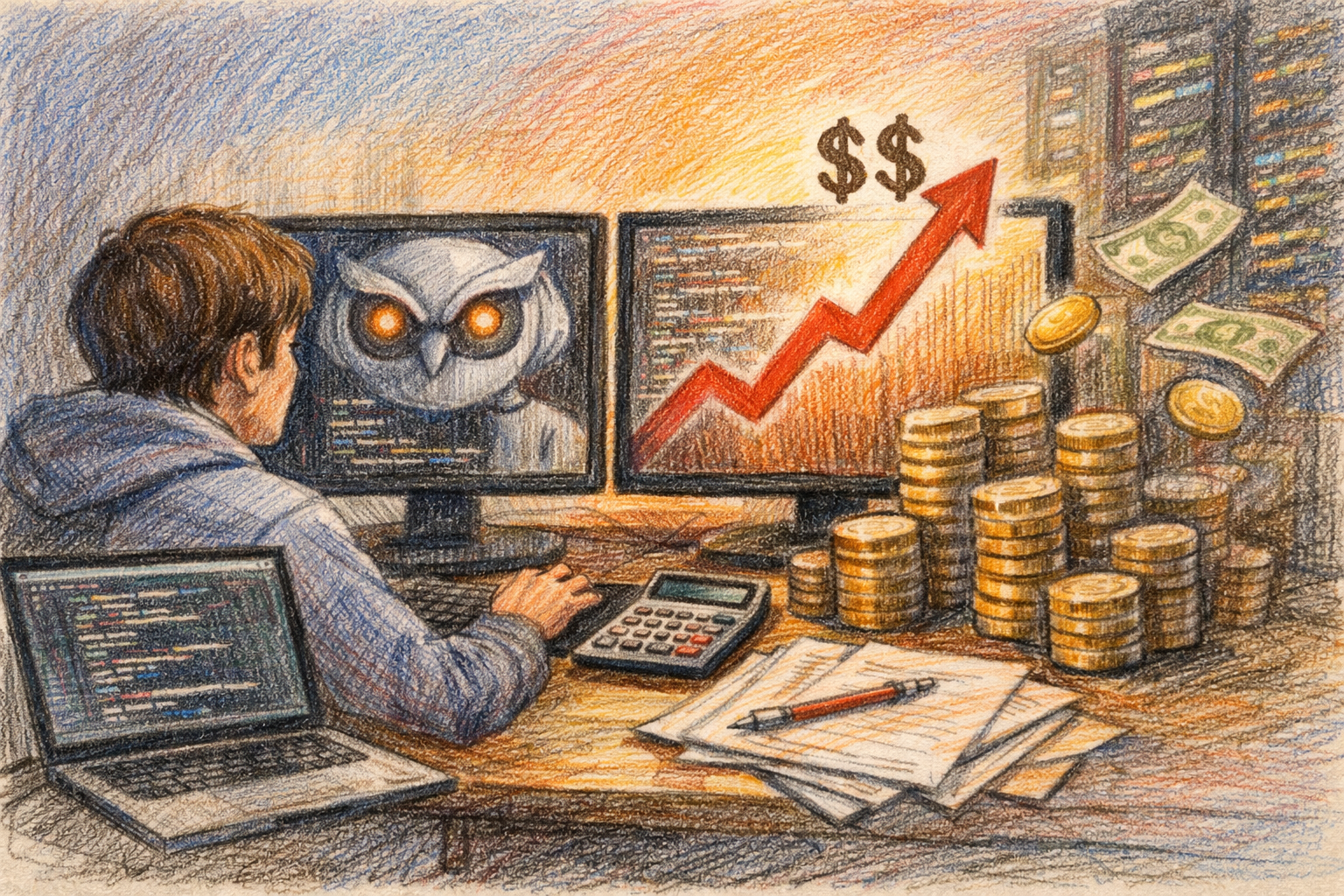
Navigating the Threat Landscape: How STIX Cybersecurity Maps the Terrain


In the dynamic world of cybersecurity, staying ahead of threats is paramount. With the increasing complexity and frequency of cyber-attacks, understanding the landscape of potential threats has become a critical component for organizations. This is where STIX (Structured Threat Information eXpression) comes into play, providing a standardized language to describe cyber threat information, enabling effective sharing and analysis.
Understanding the Threat Landscape
The threat landscape in cybersecurity encompasses the array of potential risks and vulnerabilities that an organization might face. These include various forms of malware, phishing attacks, ransomware, insider threats, and more. Navigating this landscape involves identifying, analyzing, and mitigating these threats to protect sensitive data and maintain operational integrity.
The sheer volume and sophistication of cyber threats can be overwhelming. Cybersecurity professionals need tools that help them visualize and understand these threats in a structured manner. This is essential not only for immediate response but also for long-term strategic planning.
What is STIX?
STIX (Structured Threat Information eXpression) is a standardized language developed by the cybersecurity community to represent threat information consistently. Created by the Organization for the Advancement of Structured Information Standards (OASIS), STIX enables organizations to share threat data in a format that is both human-readable and machine-processable. For those wondering, what is STIX/TAXII? it’s essential to understand that TAXII (Trusted Automated Exchange of Indicator Information) complements STIX by providing the protocols for exchanging this structured threat information.
STIX structures threat information into a cohesive format, allowing cybersecurity systems to integrate and act upon the data effectively. It facilitates a common understanding across different organizations and systems, ensuring that the threat intelligence is actionable and interoperable.
Key Components of STIX
STIX is built around several core components, each serving a specific purpose in describing threat information:
1. Indicators
These are pieces of information that suggest malicious activity. Indicators might include IP addresses, domain names, file hashes, or email addresses associated with known threats.]
2. Observables
These are measurable events or properties in the cyber environment, such as the presence of a specific file or network traffic patterns that indicate potential malicious activity.
3. Incidents
Incidents describe specific instances of malicious activity that have occurred, detailing how the attack was carried out, its impact, and the response taken.
4. Tactics, Techniques, and Procedures (TTPs)
TTPs provide detailed descriptions of how attackers operate, their methodologies, and the tools they use. Understanding TTPs helps in predicting and defending against future attacks.
5. Threat Actors
These are individuals, groups, or organizations responsible for carrying out malicious activities. Describing threat actors includes their motivations, capabilities, and historical activities.
6. Campaigns
Campaigns are coordinated efforts by threat actors to achieve a specific objective over time. They can span multiple incidents and use various TTPs.
7. Courses of Action
These are recommended actions to prevent or respond to threats. They include strategies, mitigations, and remediation steps.
How STIX Maps the Threat Landscape
STIX provides a comprehensive framework to map out the threat landscape, enabling organizations to see the bigger picture and understand how different elements of cyber threats interconnect. Here’s how it works:
1. Data Integration and Sharing
By using a standardized language, STIX allows different organizations to share threat intelligence seamlessly. This collective intelligence helps in identifying emerging threats and understanding their scope and impact.
2. Threat Detection and Analysis
With structured data, cybersecurity tools can more effectively analyze and detect threats. Indicators and observables provide the raw data needed to identify malicious activity, while TTPs offer context and deeper insights.
3. Incident Response
In the event of a cyber incident, STIX helps by providing detailed information about the incident, including the methods used and the threat actors involved. This information is crucial for an effective and timely response.
4. Strategic Planning
Understanding the methods and motivations of threat actors through STIX components like TTPs and threat actors allows organizations to plan their defenses strategically. They can prioritize resources to defend against the most relevant threats.
5. Predictive Analysis
By analyzing past incidents and campaigns, STIX enables predictive analysis. Organizations can anticipate future attacks by understanding patterns and trends in threat actor behavior.
The Importance of a Standardized Approach
One of the biggest challenges in cybersecurity is the fragmentation of data and approaches. Different organizations and tools often use varied formats and terminologies, making it difficult to share and act upon threat intelligence efficiently. STIX addresses this by providing a common language, ensuring that everyone is on the same page.
A standardized approach like STIX also facilitates automation. Cybersecurity systems can automatically ingest, analyze, and respond to threat data when it’s presented in a consistent format. This reduces the manual workload for cybersecurity professionals and allows for quicker, more efficient threat mitigation.
Real-World Applications of STIX
Several organizations and cybersecurity platforms have adopted STIX to enhance their threat intelligence capabilities. For example:
Information Sharing and Analysis Centers (ISACs)
ISACs are industry-specific organizations that collect, analyze, and disseminate threat information. Using STIX, they can share this data with member organizations in a standardized format, improving collective security.
Cyber Threat Intelligence Platforms (TIPs)
TIPs aggregate threat data from multiple sources. By leveraging STIX, these platforms can ensure compatibility and improve the accuracy and relevance of the threat intelligence they provide.
Government Agencies
National cybersecurity agencies use STIX to share threat information with critical infrastructure sectors and other stakeholders, enhancing national security.
Conclusion
In the ever-evolving threat landscape of cybersecurity, having a clear and structured understanding of threats is crucial. STIX offers a robust framework to map this landscape, enabling organizations to share, analyze, and respond to threat information effectively. By standardizing threat data, STIX not only improves the efficiency of threat detection and response but also fosters a collaborative approach to cybersecurity, where knowledge and insights can be shared across the community to strengthen collective defenses.