Anthropic’s Claude Finds 22 Firefox Vulnerabilities
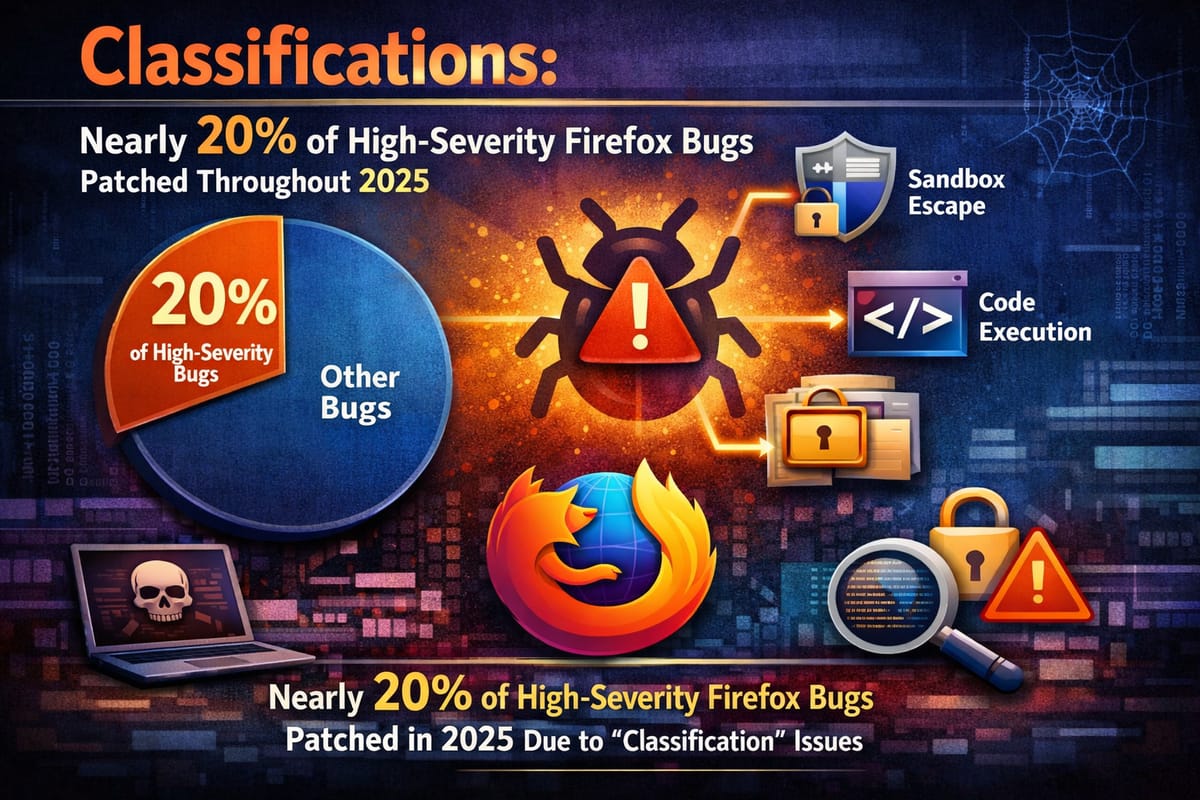
Anthropic’s Claude Opus 4.6 artificial intelligence model has discovered 22 security vulnerabilities in the Firefox web browser during a two-week collaboration with Mozilla that took place in January 2026. Fourteen earned high-severity classifications, which is almost 20% of all high-severity Firefox bugs patched throughout 2025. Mozilla validated the findings and shipped fixes in Firefox 148, which was released late last month.
Discovery Process and Methodology
Anthropic’s Frontier Red Team contacted Mozilla in late February after Claude flagged bugs in Firefox’s JavaScript engine. The AI-driven research effort proved remarkably efficient. After just twenty minutes of exploration, Claude Opus 4.6 reported that it had identified a Use After Free (a type of memory vulnerability that could allow attackers to overwrite data with arbitrary malicious content) in the JavaScript engine.
By the end of this effort, we had scanned nearly 6,000 C++ files and submitted a total of 112 unique reports, including the high- and moderate-severity vulnerabilities mentioned above. Of the 112 total reports Anthropic submitted, Mozilla issued 22 CVEs for security-sensitive bugs, including 14 rated high severity. The remaining roughly 90 reports involved non-security issues such as crashes and logic errors.
We chose Firefox because it’s both a complex codebase and one of the most well-tested and secure open-source projects in the world. This makes it a harder test of AI’s ability to find novel security vulnerabilities than the open-source software we previously used to test our models.
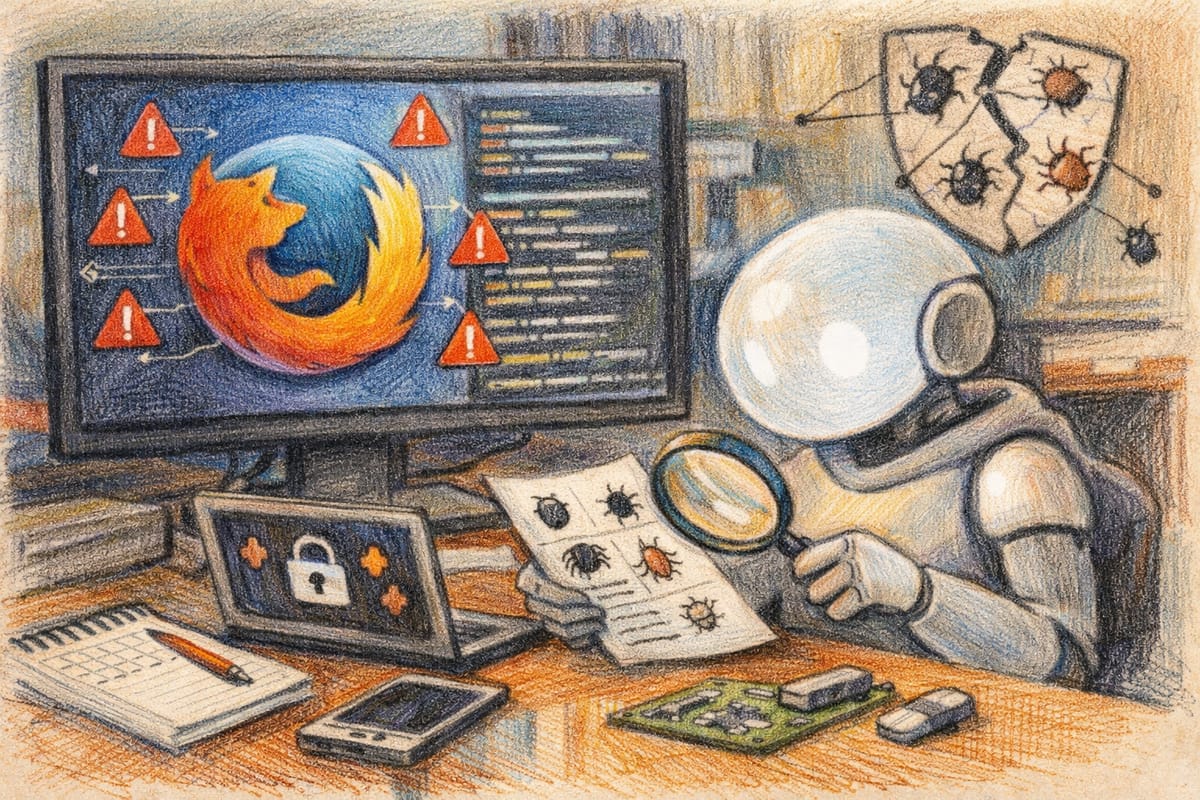
Exploit Development Attempts
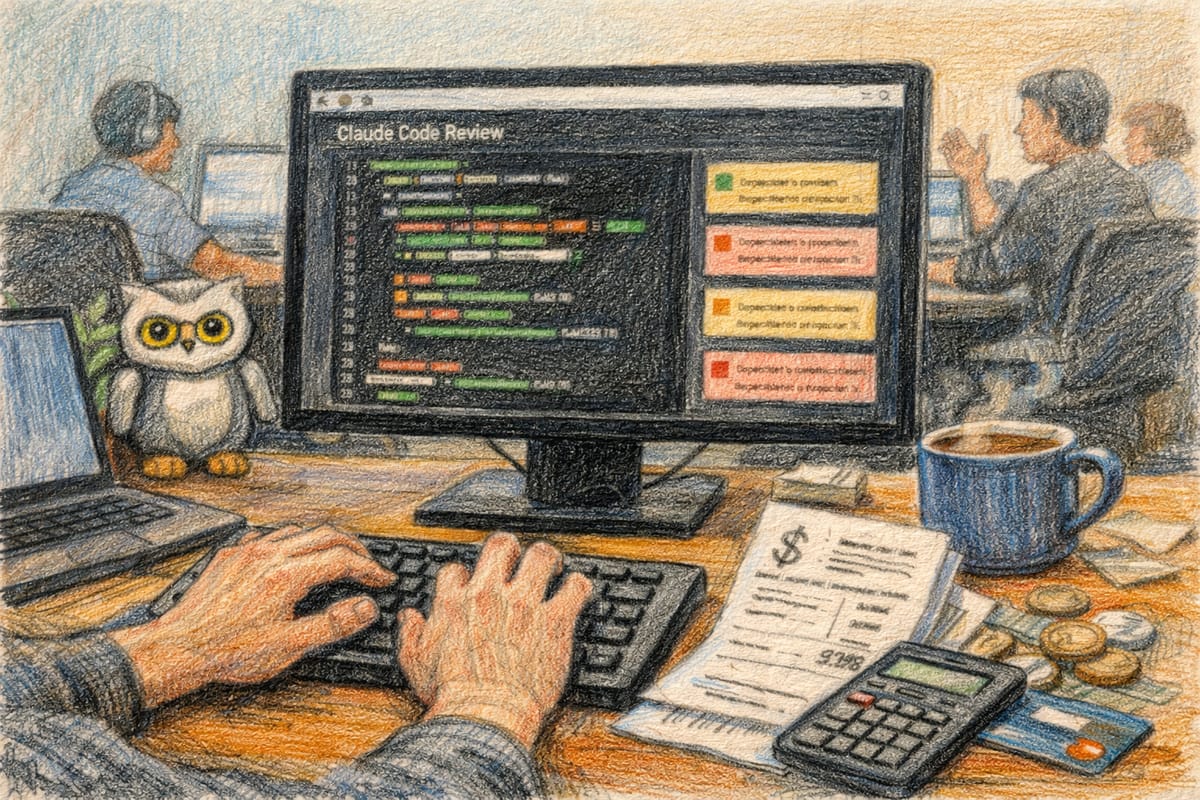
While Claude excelled at identifying vulnerabilities, the AI model struggled significantly when attempting to weaponize them into working exploits. The team ended up spending $4,000 in API credits trying to concoct proof-of-concept exploits, but only succeeded in two cases.
One successful exploit targeted CVE-2026-2796, a JIT miscompilation in the JavaScript WebAssembly component. In a detailed technical analysis, Anthropic’s security researchers reverse-engineered Claude’s exploit, which exploited a type confusion vulnerability involving Function.prototype.call.bind() wrappers. The vulnerability allowed Claude to develop exploitation primitives, including ‘addrof’ (leak an object’s address) and ‘fakeobj’ (forge a JavaScript object reference to an arbitrary address). Claude then used these to create a fake ArrayBuffer for arbitrary read/write access, ultimately achieving code execution.
However, the exploit only worked in a testing environment that intentionally removed some security features, including Firefox’s sandbox. Claude isn’t yet writing “full-chain” exploits that combine multiple vulnerabilities to escape the browser sandbox, which are what would cause real harm. And recall that Opus 4.6 only turned a vulnerability into an exploit in two cases (given hundreds of chances at dozens of bugs).
Security Implications and Dual-Use Concerns
Anthropic stated that frontier language models are now world-class vulnerability researchers, but cautioned that “looking at the rate of progress, it is unlikely that the gap between frontier models’ vulnerability discovery and exploitation abilities will last very long.”
We believe this suggests motivated attackers who can work with LLMs will be able to write exploits faster than ever before. The finding has both positive and concerning implications for cybersecurity. The disparity between Claude’s vulnerability discovery and exploitation capabilities gives defenders a temporary advantage.
This is a moment to move quickly—to empower cyberdefenders to secure as much code as possible in order to raise the skill level required for cybercriminals to misuse LLMs’ cyber capabilities. We urge developers to take advantage of this window to redouble their efforts to make their software more secure.
Mozilla’s Response and Integration
Mozilla has already started integrating AI-assisted analysis into its internal security workflows. As part of this collaboration, Mozilla fielded a large number of reports from us, helped us understand what types of findings warranted submitting a bug report, and shipped fixes to hundreds of millions of users in Firefox 148.0.
Claude Opus 4.6 found 22 vulnerabilities in February 2026, more than were reported in any single month in 2025. This dramatic acceleration demonstrates the potential impact of AI-assisted security research on open-source software development and security patching cycles.
Key Facts
- The vulnerabilities were identified over a two-week period in January 2026.
- Claude Opus 4.6 found 22 security vulnerabilities in Firefox in just two weeks. Fourteen earned high-severity classifications, which is almost 20% of all high-severity Firefox bugs patched throughout 2025.
- By the end of this effort, we had scanned nearly 6,000 C++ files and submitted a total of 112 unique reports.
- After approximately $4,000 in API credits and hundreds of attempts, Claude successfully created exploits in two cases.
- Mozilla validated the findings and shipped fixes in Firefox 148.
- We repeated our experiment with Opus 4.1, Opus 4.5, Sonnet 4.5, Sonnet 4.6 and Haiku 4.5, but none succeeded.
Sources
- InfoQ: AI Model Discovers 22 Firefox Vulnerabilities in Two Weeks
- Anthropic: Partnering with Mozilla to improve Firefox’s security
- Anthropic Red Team: Reverse engineering Claude’s CVE-2026-2796 exploit
- TechCrunch: Anthropic’s Claude found 22 vulnerabilities in Firefox over two weeks
Sources
- AI Model Discovers 22 Firefox Vulnerabilities in Two Weeks – InfoQ
- Anthropic Finds 22 Firefox Vulnerabilities Using Claude Opus 4.6 AI Model
- Partnering with Mozilla to improve Firefox’s security
- Anthropic’s Claude uncovers 22 Firefox security vulnerabilities
- Anthropic’s Claude found 22 vulnerabilities in Firefox over two weeks | TechCrunch
- Reverse engineering Claude’s CVE-2026-2796 exploit