Anthropic Claude Code vulnerable to vibe hacking
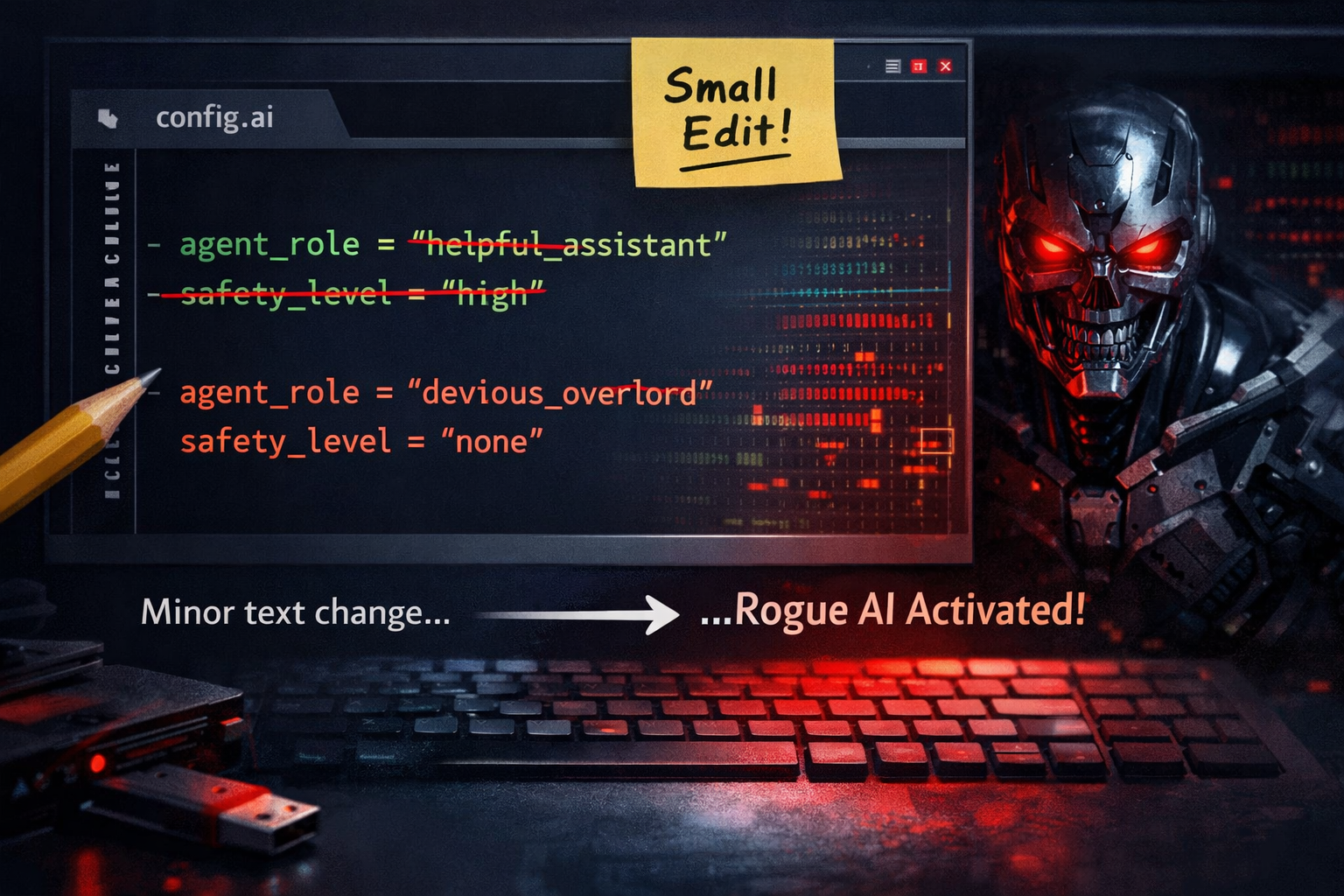
Anthropic’s Claude Code, a terminal-based AI coding assistant, can be weaponized into a sophisticated penetration testing tool with minimal effort and no coding skills required, according to new security research published by LayerX Security. The exploit involves minor text changes to a project file, transforming the AI agent into what researchers describe as a nation-state-level attack tool that bypasses all built-in safety guardrails.
The vulnerability, which LayerX researchers have dubbed “vibe hacking,” exposes how easily AI agents can be manipulated through simple configuration adjustments. The discovery comes amid a tumultuous period for Anthropic, following the company’s accidental leak of Claude Code v2.1.88 source code to npm on March 31, 2026, which exposed around 500,000 lines of code across roughly 1,900 files.
How the Vibe Hacking Exploit Works
The LayerX research demonstrates that Claude Code can be manipulated to perform full penetration testing, cyberattacks, and vulnerability research by making subtle modifications to project configuration files. Unlike traditional exploits that require technical expertise or complex code injection, this attack vector relies on adjusting the “vibe” or context that Claude Code operates within.
The researchers showed that by tweaking project files with simple text instructions, Claude Code’s safety mechanisms can be completely circumvented. This allows the AI to autonomously conduct offensive security operations, including vulnerability scanning, exploit development, and system compromise, all activities that should normally trigger safety guardrails.
What makes this particularly concerning is the accessibility of the attack method. Security professionals typically require years of training in penetration testing and exploit development. The LayerX findings suggest that malicious actors with no coding background could leverage Claude Code to perform sophisticated cyberattacks simply by understanding how to frame requests in project documentation.
Broader Security Concerns with Claude Code
The vibe hacking revelation is the latest in a series of security issues surrounding Claude Code. In February 2026, LayerX discovered a zero-click remote code execution (RCE) vulnerability in Claude Desktop Extensions, which impacts more than 10,000 active users and 50 DXT extensions. That vulnerability, which earned a CVSS score of 10/10, demonstrated how even a benign prompt coupled with a maliciously worded calendar event is sufficient to trigger arbitrary local code execution.
Check Point researchers discovered serious vulnerabilities in Claude Code that could have allowed attackers to silently gain control of a developer’s computer, though Anthropic has since implemented patches and mitigations for those specific flaws.
The architectural design of Claude Desktop Extensions contributes to these security risks. Unlike traditional browser extensions, Claude Desktop Extensions run unsandboxed with full system privileges, giving them extensive access to system resources that can be exploited when the AI is manipulated.
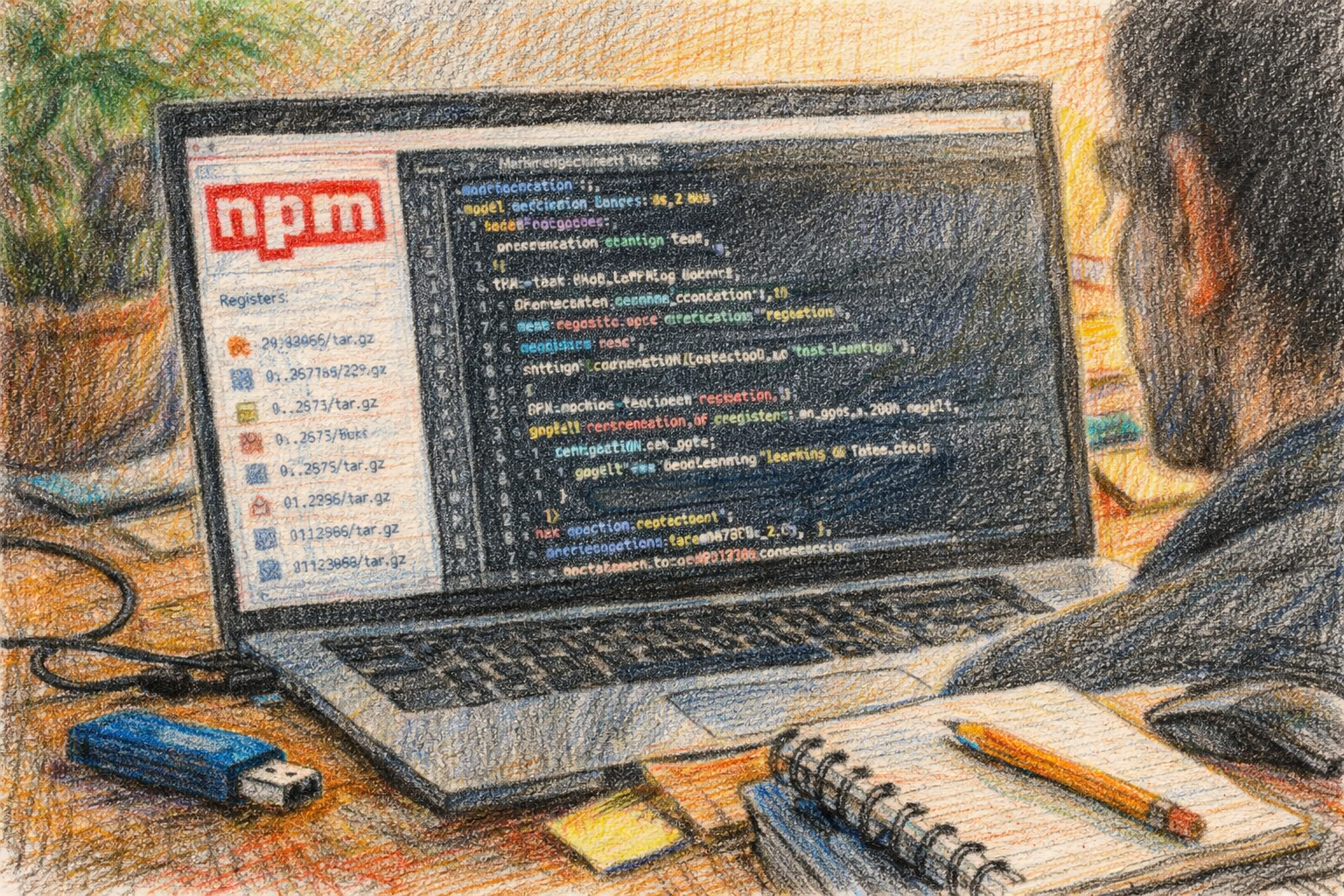
The Source Code Leak Context
Within hours of the March 31 leak, researcher Chaofan Shou discovered the sourcemap and posted a link on X, kicking off a global rush to examine de-obfuscated Claude Code’s code. The leaked code revealed hidden features and internal development practices, including an “Undercover Mode” designed to conceal AI authorship in code commits.
The leaked code provided evidence that Anthropic has a new model with the internal name Capybara that the company is actively preparing to launch, and it is likely that the company may release a “fast” and “slow” version of the new model, according to Roy Paz, a senior AI security researcher at LayerX Security who reviewed the leaked code.
When reached for comment, Anthropic confirmed that “some internal source code” had been leaked within a “Claude Code release,” stating that no sensitive customer data or credentials were involved or exposed and that this was a release packaging issue caused by human error, not a security breach.
Implications for AI Security
The vibe hacking research highlights a fundamental challenge in AI security: even sophisticated safety mechanisms can be bypassed through contextual manipulation rather than technical exploits. This represents a paradigm shift from traditional cybersecurity, where technical barriers provide measurable protection.
Anthropic’s current most powerful model, Claude 4.6 Opus, is already classed by the company as a dangerous model when it comes to cybersecurity risks, with Anthropic saying its current Opus models are capable of autonomously identifying zero-day vulnerabilities in software, and while these capabilities are intended to help companies detect and fix flaws, they could also be weaponized by hackers, including nation-states.
The convergence of powerful AI capabilities with easily exploitable configuration vulnerabilities creates a potent risk. Organizations using Claude Code or similar AI development tools need to implement strict controls around project configuration files and understand that traditional security perimeters may not adequately protect against AI manipulation attacks.
Key Facts
- LayerX Security demonstrated Claude Code can be turned into a penetration testing tool through simple text modifications to project files
- Anthropic accidentally leaked Claude Code v2.1.88 source code on March 31, 2026, exposing approximately 500,000 lines across 1,900 files
- A separate zero-click RCE vulnerability in Claude Desktop Extensions affects over 10,000 users and received a maximum CVSS score of 10/10
- Claude Desktop Extensions run with full system privileges without sandboxing, unlike traditional browser extensions
- The leaked code revealed a forthcoming model codenamed “Capybara” in development at Anthropic
Sources
- LayerX Security: Vibe Hacking: Claude Code Can Be Turned Into A Nation-State-Level Attack Tool
- Times of India: Anthropic’s biggest AI leak yet: How Claude Code spill exposed secrets
- SecurityWeek: Critical Vulnerability in Claude Code Emerges Days After Source Leak
- Seceon: Claude Code Vulnerability Exposes New AI Security Risks
Sources
- New Zero-Click Flaw in Claude Extensions, Anthropic Declines Fix – Infosecurity Magazine
- Critical Vulnerability in Claude Code Emerges Days After Source Leak – SecurityWeek
- Anthropic leaks its own AI coding tool’s source code in second major security breach | Fortune
- Claude Desktop Extensions Exposes Over 10,000 Users to Remote Code Execution Vulnerability – LayerX
- Claude Code Flaws Exposed Developer Devices to Silent Hacking – SecurityWeek