5 Ways Unsecure File Sharing Services Can Hamper Your Business

Cloud computing has allowed the world to share files with anyone living anywhere in the world in seconds. However, it also increases the risk of data breaches, which can cause significant issues for an organization, including lost revenue, litigation, compliance violations/penalties, and brand erosion.
Insecure file sharing systems can expose businesses to unauthorized access by organized crime syndicates, rogue nation-states, competitors, and other bad actors. Kitetoons by Kiteworks takes a lighthearted look at what can happen when organizations share files insecurely.
Therefore, it’s best to avoid sharing files insecurely.
Here in fact are five ways a lack of secure file sharing services can hamper your business:
-
Losing Critical, Confidential Information
A business organization is bound to have important financial data, product plans, and strategic plans for future development and growth.
This information is crucial to a business’s performance and success. Should this information be leaked or intercepted when being shared internally or externally, the consequences could be catastrophic.
Imagine a competitor getting access to your product roadmap or market expansion plans. They could use this information to their advantage by copying your ideas, entering a new market before you, or signing exclusivity agreements with your prospective partners. By the time you learn about the breach, it may be too late.
It’s important therefore to take the necessary steps ahead of time to prevent a corporate espionage disaster like this. How?
You should always be vigilant about where your sensitive information is stored, who has access to it, when they access it, and who they share it with. Monitoring this activity closely can help you avoid—or at least identify—a breach. A secure file sharing service that encrypts messages and attachments helps to ensure hackers cannot intercept and access your business’s most critical information.
-
Susceptibility to Malware
Data-driven Private Content Network, Kiteworks has published a Forecast Report for 2023, which shows organizations will focus more resources on security hardening, and malware is one of the most important reasons.
A typical organization receives hundreds, if not hundreds of thousands, of inbound emails every day. Many are legitimate communications from customers, partners, and service providers,; however, many more are unsolicited. Unfortunately, these emails can contain viruses and malware that can cause a range of minor to major disruptions to your business.
If an unsuspecting employee clicks on a suspicious link or attachment, it can unleash a chain of events that can ultimately lead to a data breach. Once again, a data breach can have short- to long-term implications, including loss of business, litigation, compliance violations and fines, and brand erosion.
-
Losing Personal Information
Personally identifiable information (PII) can come in different forms, such as names, email addresses, and Social Security numbers but also behavioral data, geolocation, and biometric data. Any data that relates to you personally can be considered PII.
When an organization hires an employee, it collects lots of that employee’s PII. The organization will in fact generate additional PII, like insurance information, salary, bonuses, employee ID numbers, and more. This data is not only stored in the organization’s human resources information system (HRIS) but also shared with external partners like payroll processors, insurance providers, and business consultants.
This highly sensitive information is highly sought after by identity thieves. When hackers intercept this information as it’s shared between an organization and its partners, it typically is marketed on the dark web where identity thieves can buy it to create financial havoc, costing victims tens to hundreds of thousands of dollars in fraudulent expenses. Getting these charges reversed and clearing your name (and credit) can take months or even years. Once again, a secure file sharing service that encrypts messages and attachments containing PII will help ensure this sensitive information never falls into the wrong hands and winds up on the dark web.
-
Third-party Insecure Network
Digital supply chain risk or third-party risk is a leading source of information loss for organizations. Organizations are reliant upon hundreds or even thousands of partners, vendors, and suppliers. An organization may have a big cybersecurity budget, supported by data security processes and procedures for its employees; however, that organization’s partners may have significantly fewer cybersecurity resources. Because of the interdependence between an organization and its partners, a weak “link” in the digital supply chain can impact the entire ecosystem.
Cyberattacks are well aware of this disparity. These attackers in fact frequently engage in “island hopping,” a type of cyberattack in which an attacker targets multiple, interconnected systems in order to gain access to a system that is not directly accessible from the attacker’s initial entry point. Basically, the attackers will use a variety of tactics, including phishing, to identify a vulnerability of one organization to gain entry into other organizations throughout the supply chain.
This type of attack emphasizes the need for connected systems to have rigorous security measures in place to protect them from intrusions. A secure file sharing system that doesn’t require opening a port for each and every partner is a great way to manage digital supply chain risk.
-
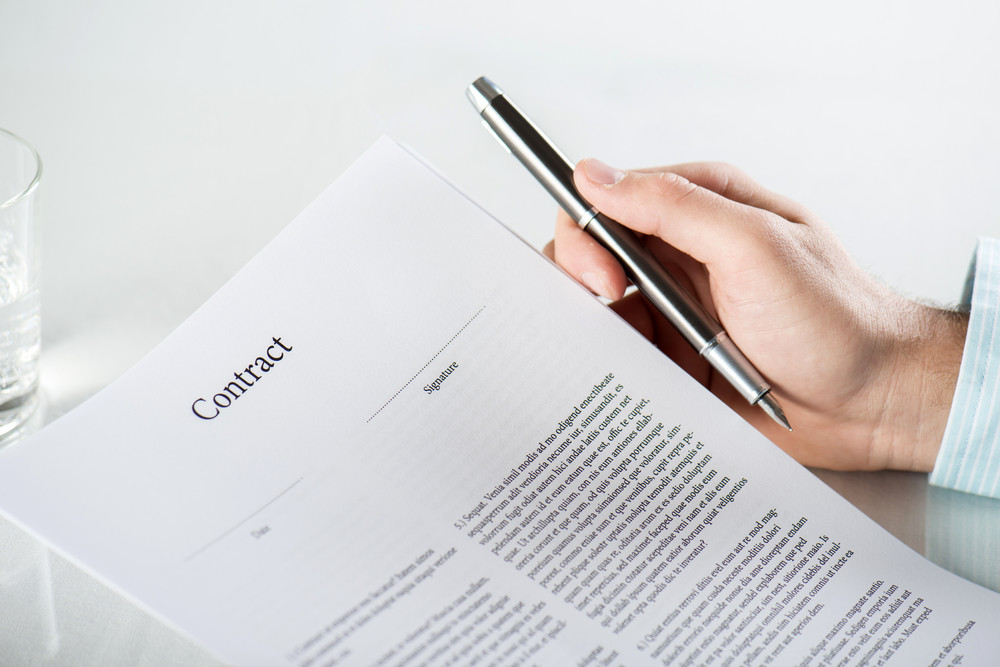
Compliance Violations
In recent years, data protection laws, such as the California Consumer Privacy Act (CCPA) or the General Data Protection Regulation (GDPR) have emerged, requiring organizations to protect their customers’ privacy or face costly fines and penalties.
If an organization engages in insecure file sharing practices, including using insecure file sharing solutions, it can ultimately lead to a data breach and subsequent compliance violation, particularly for organizations operating in highly regulated industries like healthcare, government, and financial services.
Unsecure data file sharing practices can include sending unencrypted messages and files, not requiring senders and recipients to authenticate before accessing sensitive information, or using a file sharing or storage solution that does not have adequate security measures in place. For example, if a file is uploaded to a file sharing service with no encryption, anyone with access to the service can see what data has been uploaded. This puts sensitive information—and the organization—at risk. Additionally, if an organization doesn’t require multi-factor authentication, an unauthorized employee or bad actor could gain access to the file sharing solution. This puts the data stored on the solution at risk of theft and misuse, which is a data privacy compliance violation.
The financial, legal, and business repercussions of a data privacy compliance violation can be severe. A violation can result in the company being heavily fined from regulatory bodies entrusted with enforcing GDPR, CCPA, HIPAA, IRAP, PIPEDA, and other regulations. In addition to financial penalties, an organization can also face reputational damage from the violation, which can affect its ability to retain existing and acquire new customers. Lastly, the organization can be held liable for any damages suffered by customers due to the data breach, which can cost multiple millions of dollars.
Organizations that use secure file sharing practices, solutions, and processes repeatedly demonstrate compliance with data privacy regulations. Organizations can also implement policies and processes around their file sharing solution to ensure data privacy compliance, including a data classification system, user education and training, and regular audits. With these measures in place, the organization can be assured that it is compliant with data privacy regulations.
Some Parting Advice
Organizations must use secure file sharing solutions, policies, and processes to protect their critical information from unauthorized access. It is the only way a business can avoid costly compliance violations and litigation but also ensure they protect their employees, customers, intellectual property, and long-term viability.