The introduction of the World Wide Web in the 90s has brought new possibilities and opened up vast opportunities. However, it also brought with it several downsides of connectivity. A threat known as computer hacking could infiltrate your software, steal your personal information, and trick you into revealing your private data. Therefore, it is crucial that your business software systems and secure and protected.
It is not enough to invest in the best software systems. You also need to invest in multiple security tools before you can begin to enjoy a return on your software systems investment. So, here are some ways to keep your software systems secure.
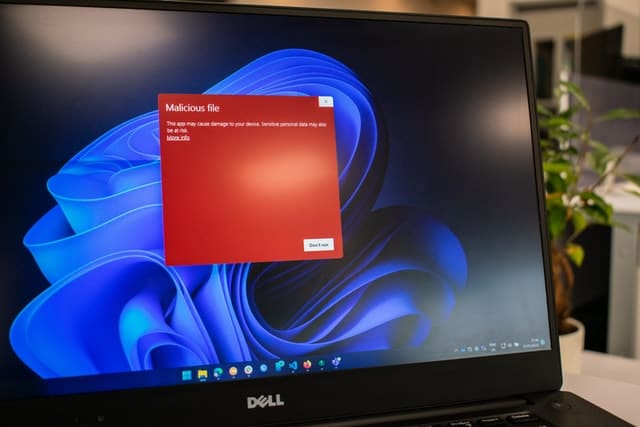
One of the most effective ways to keep your software systems safe is installing antivirus and malware protection and keeping it up to date. The antivirus software is designed to identify, prevent, and prevent malicious software from attacking your computer system, especially viruses. No matter how careful you are in using your computer, the virus can still find ways to attack. Thus, antivirus software should be part of your systems security strategy.
The antivirus software will run in the background and check every file you open, then compare it to any known viruses and other types of malware to prevent your computer from getting infected. It will also perform a system scan to ensure that no viruses are lying somewhere on your computer. If it comes across a virus, it will prevent the file from running and will either automatically delete it or ask you to run it in case of false detection.
Antivirus protection is essential to protect your data and computer systems from getting corrupted. The antivirus software works like a security person at the gate that prevents unwanted entry. Remember, prevention is always better than cure. So, it is best to have a system in place designed to identify and prevent potential virus attacks than spending money later on to repair infected computer systems.
Embedded systems security offers mechanisms to keep an embedded system protected from malicious attacks online. It's a field of cybersecurity that focuses on preventing unwanted access and use of embedded systems. Companies implementing embedded systems security may also consider bringing in an embedded software engineer who can help ensure that the embedded system has the necessary security mechanisms to mitigate any damages from these malicious attacks.
There are two types of security on the embedded security systems - software and physical security. The software security manages and responds to any malicious behavior in the system during the initialization process and run time. Features include firewall network traffic, device authentication, and strict hardening of system software. Meanwhile, physical security can refer to surveillance cameras and locked doors to keep unauthorized persons from getting into the embedded system, either stealing or physically damaging it. Physical security helps restrict access to the equipment and other sensitive areas in the embedded system.
Most embedded systems carry out mission-critical and safety-critical functions vital to their intended function and surrounding environment. Embedded systems security is applicable to various industries, from household appliances to aerospace and defense.
Companies invest a lot of money and time for their computer systems to remain safe and secure. Those who are extremely security-conscious might even have their own security operations center. Of course, they also have antivirus tools and firewalls. But only a few companies have given much thought to the important aspect of their digital operations - the operating systems. Others won't even think about security when deciding on the operating system to use.
But which operating system is considered the most secure? When it comes to security, Linux tops the list. Compared to other operating systems, it is secure and highly reliable. Linux and Unix-based Operating Systems have fewer security flaws since several developers constantly review the code. Also, anyone has access to its source code. As a result, you will not require any antivirus software to protect your computer against viruses and malware. Linux is secure because it's open-source, which means you have access to its source code. As a result, any bugs in the Linux Operating System can be fixed rapidly, unlike some other operating systems. It’s wise if you decide to move to a new operating system that you bring in a Linux software engineer. This can be easily achieved by working with a specialist Linux recruitment agency that can also walk you through the transition.
Another reason why Linux is a great choice for an operating system is you'll have full control when updating your computer system. Also, the system updates are immensely faster with Linux and allow you to update the system at any time or not at all, depending on what you prefer. But with operating systems like Windows, you will sometimes be forced to update the system even if you don't want to.
Another important tip to keeping your software systems secure is to use strong passwords. Make sure you and everyone involved in your business operations use strong passwords. This applies to all computers and gadgets, including tablets, laptops, and smartphones. Most importantly, keep email accounts safe and secure by using strong passwords and changing them frequently.
When it comes to creating a strong password, avoid using personal information. It must not also include references to your birthday, name, phone number, or address. Also, try to incorporate symbols, letters, and numbers. Include a variety of random characters, letters, and numbers to make the password more complex. When it comes to the length of the password, it should contain at least 16 characters. It can help minimize your chances of becoming a victim of cyber-attacks and data breaches.
Avoid repeating passwords. Reusing passwords for different accounts is a common mistake and will put you at risk of credential stuffing attacks, which is common for cybercriminals. Also, avoid using real words. Hackers are fond of using malicious programs capable of processing every word in the dictionary to crack passwords. Try to avoid using proper nouns and some other standalone words in the dictionary that will make it easier for cybercriminals to decode. Use the above techniques to keep your business software systems secure.