The Best Practices For Managing IT Security


Any person may be a victim of a cybercrime. If you have ever had someone steal your debit card number, you’ve been a victim. Business owners have watched colleagues fall victim to ransomware attacks, and young children have had their social security numbers stolen. Often, they don’t learn of this theft until they are adults. Thanks to the prevalence of these crimes, every person should know how to protect themselves from cybercriminals. Businesses, in particular, must know cybersecurity best practices through managing IT security.
A security breach could lead to major financial losses not to mention damage to the company’s reputation. Although it is impossible to protect against all cyberattacks, as criminals find new ways to breach systems regularly, a company can and should take steps to protect against the attacks. How can it do so? The following best practices should be implemented by all companies today. If you need help with managing your IT security, a managed services provider can assist you with these tasks.
Software Updates
Set software updates to happen automatically. Many people assume software developers only provide updates to fix known issues or add new features. These updates, however, are frequently needed to upgrade security and fix any gaps in the system that would allow cybercriminals access to sensitive information. Updating the software helps eliminate vulnerabilities.
Check Links Before Clicking
Hyperlinks are very common today. They help you navigate the internet without having to type in URLs regularly. However, some links aren’t what they seem. Before you click on a hyperlink, hover over it. Doing so allows you to see which site you will arrive at and whether it is reputable.
Delete Suspicious Emails
Many people delete emails from unknown senders. Cybercriminals recognize this and have found ways to send emails that appear to come from trusted senders. When opening an email, look for anything unusual. Don’t open attachments or links unless you were expecting to receive them. Ask before opening if you didn’t know the link or attachment was being sent. These are common phishing scams that many people fall for.
Password Security
Every person does it. They reuse the same password on multiple sites and never change these passwords. Cybercriminals love this because it gives them easy access to a person’s information. Once they learn this password, they can collect large amounts of data quickly and easily. Create passwords that are difficult to guess and contain letters, numbers, special symbols, and more. In addition, change these passwords regularly to keep cyberattacks to a minimum.
Hardware Updates
Your software isn’t the only thing that needs to be updated regularly. Outdated hardware may not be able to support software updates, leaving the system vulnerable to attack. Furthermore, if you fall victim to an attack, it may take longer to recover if you have older hardware. Keep this in mind and budget for regular hardware upgrades to reduce the risk of these attacks.
Turn Bluetooth Off
If you aren’t using Bluetooth at the moment, turn it off. This feature found on many devices offers another way for cybercriminals to enter your systems. Reduce the risk of unauthorized entry by turning Bluetooth off when it is not in use.
Choose a File-Sharing Solution Wisely
Many companies use file-sharing solutions today. If confidential information is being shared, this solution must use encryption to ensure the information doesn’t fall into the wrong hands. A person might assume all solutions have this feature, but that is not the case.
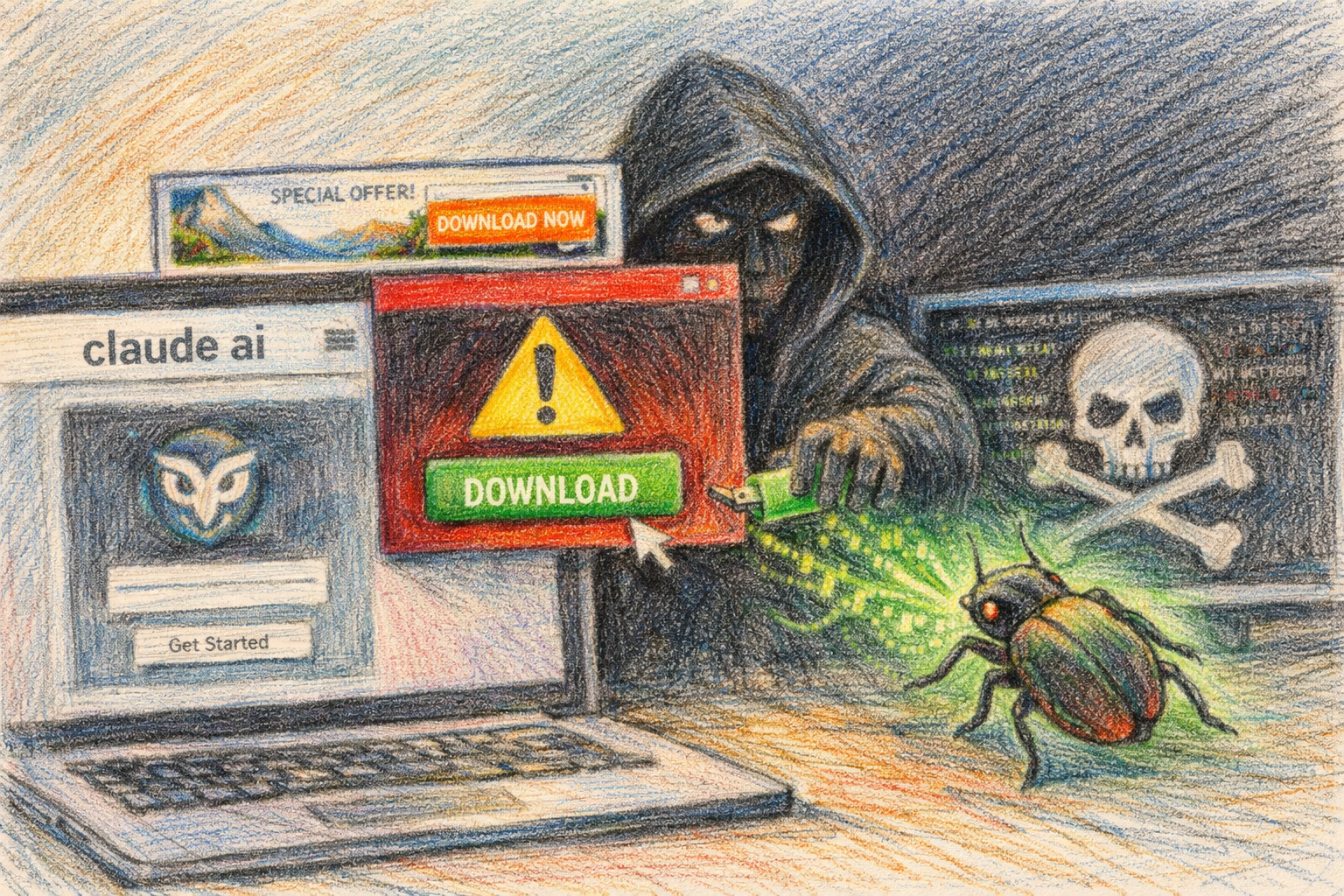
Install Anti-Virus and Anti-Malware Programs
Any time your device is connected to the internet, malware is a concern. While you cannot eliminate this threat, steps can be taken to minimize it. Invest in robust anti-virus and anti-malware programs to achieve this goal.
Two-Factor Authentication
Two-factor authentication is annoying in the eyes of many. Nevertheless, it helps keep sensitive information safe, so you should use it whenever possible. It adds another layer of protection by requiring you to verify your identity before accessing this information.
Work With a White-Hat Hacker
Hire a hacker to keep your information safe. White-hat hackers work to uncover security gaps and boost your cybersecurity efforts. They will find risks in the managing IT system and security that you may not be aware of.
Website Security
When creating a website, install an SSL certificate and enable HTTPS. Doing so ensures all information shared between the website server and the visitor’s browser is encrypted. If visiting a website, look for HTTPS before sharing sensitive information.
External Device Scans
Many people scan their internal storage devices regularly to remove viruses, malware, and more. They never stop to do the same with external storage devices though. These threats can spread when devices are connected, so scan external devices regularly along with internal storage devices.
Online Storage
Never store information online in an unsecured location. Part of managing IT security is putting this information in a place where only authorized users can see it. Doing so will help protect you from cybercriminals.
Scan for Adware
Scan for adware and remove it from your devices. These programs help deliver targeted ads to consumers. However, they threaten your privacy, so they should be removed.
No Public Networks
People often appreciate having access to a hotspot or public network when they are on the go. This hotspot or network allows them to stay connected to others. Public networks are also breeding grounds for cyberattacks. Any information shared on one of these networks can be seen by anyone else connected to the same network. If you must use a public network, use a VPN.
Conduct Regular Backups
The most important thing you can do to protect yourself is regularly back up data. If a cyberattack occurs, this backup allows you to recover in less time. You won’t need to worry about any information being lost because you secured it in a separate location.
Many people assume they are doing enough to protect themselves from cyber threats. In actuality, unless a person has gone completely off the grid and has no electronic devices, they are at risk. Ask any major corporation. They spend countless dollars each year to protect themselves from attacks and yet still fall victim. You are no different. Implement these best practices today and have peace of mind you are doing everything possible to keep you or your organization safe.